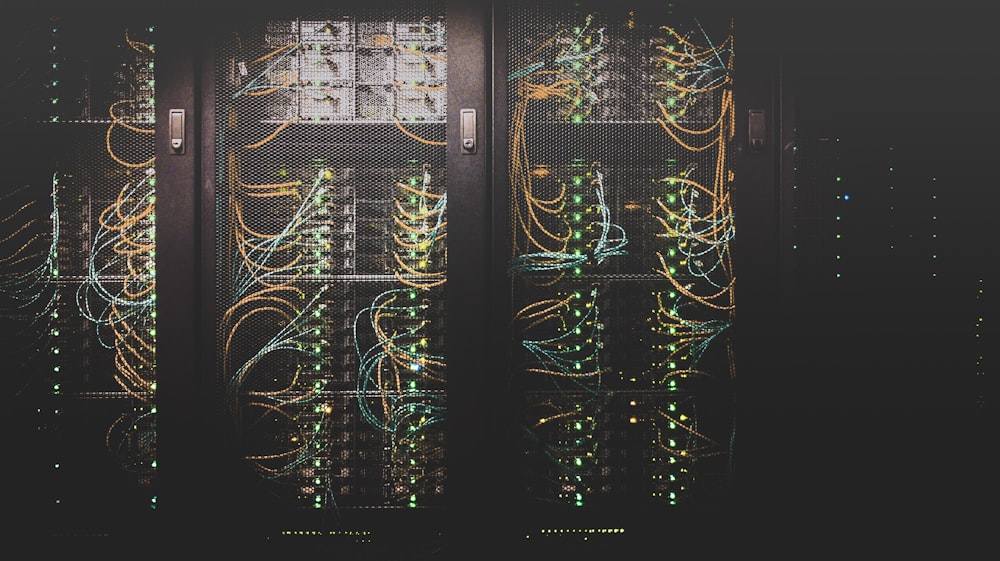
In the rapidly evolving landscape of enterprise resource planning (ERP) and business operations management, the shift from localized, "on-premise" installations to cloud-based solutions has changed more than just where data lives. It has fundamentally altered the architecture of how software is delivered and secured. At the heart of this transformation lies multi-tenant architecture, a design philosophy that allows multiple organizations (tenants) to share the same computing resources while keeping their data strictly isolated and secure.
For business leaders, understanding multi-tenancy isn't just a technical requirement—it is a strategic necessity. Whether you are migrating to a new ERP or scaling your current operations, the way your system handles data isolation determines your security posture, your cost efficiency, and your ability to scale.
Understanding the Multi-Tenant Ecosystem
To visualize multi-tenant architecture, imagine a modern high-rise office building. While every business in the building shares the same foundation, plumbing, and electrical grid (the infrastructure), each business has its own locked suite with private files and restricted access (the data isolation).
In contrast, a single-tenant architecture is like a detached house. It offers total privacy but requires the owner to manage everything—from the roof to the driveway—at a much higher cost. In the enterprise software world, multi-tenancy allows providers to push updates to thousands of users simultaneously, ensuring everyone is on the latest version without the friction of individual upgrades.
The Three Pillars of Data Isolation
The primary concern for any executive moving to a shared environment is security: “Can Tenant B see Tenant A’s financial reports?” The answer lies in robust data isolation strategies. Modern systems typically employ one of three models:
1. Database-per-Tenant: Each customer has their own physical database. This offers the highest level of isolation but is the most difficult to scale.
2. Schema-per-Tenant: All tenants share a database, but each has a private "schema" or logical container. This balances security with resource management.
3. Shared Schema (Row-Level Security): All tenants share the same database tables. A "Tenant ID" identifies every row of data. Modern ERPs often use this for its incredible scalability, relying on sophisticated Row-Level Security (RLS) to ensure users only see what belongs to them.
Why Multi-Tenancy Matters for Your Bottom Line
For a business operating in competitive markets, the architectural choice of your software provider impacts several key areas:
1. Cost Efficiency and ROI
By pooling resources, multi-tenant systems significantly lower the "Total Cost of Ownership" (TCO). You aren't paying for an entire server that sits idle 50% of the time; you are paying for the slice of resources you actually use. These savings are usually passed down to the business in the form of lower subscription fees.
2. Seamless Scalability
In a traditional system, scaling often requires manual hardware upgrades. In a multi-tenant cloud environment, resources are elastic. Whether you are processing 100 transactions or 1,000,000, the underlying architecture absorbs the load without requiring a migration.
3. "Day Zero" Security and Updates
In a multi-tenant system, when a security patch is released, it is applied to the core infrastructure and benefits all tenants instantly. This eliminates the "lag time" associated with manual software updates, which is often when systems are most vulnerable to cyber threats.
Best Practices for Data Isolation in Enterprise Systems
If you are evaluating or building an enterprise-grade solution, keep these best practices in mind:
- Encryption at Rest and in Transit: Ensure that even if data is physically co-located, it is encrypted using tenant-specific keys.
- Strict Identity Management: Use robust Multi-Factor Authentication (MFA) and Role-Based Access Control (RBAC) to define who can see what within your specific tenant environment.
- Compliance-First Design: For businesses in finance or healthcare, ensure the architecture meets regional standards like GDPR or HIPAA. Microsoft's documentation on multi-tenant patterns provides excellent deep dives into these regulatory considerations.
- Performance Monitoring: Ensure the system has "noisy neighbor" protection, preventing one tenant's heavy data processing from slowing down your operations.
The Future: Intelligent Isolation
As we move further into the era of AI-driven business management, multi-tenant architectures are becoming even more sophisticated. We are seeing the rise of Virtual Private Clouds (VPCs) and hybrid models that offer the cost benefits of sharing while providing the "air-gapped" security once reserved for the most expensive single-tenant systems.
For modern enterprises, the goal is no longer just to store data, but to do so in a way that is agile, secure, and cost-effective. Multi-tenancy is the engine that makes this possible, allowing businesses to focus on growth rather than server maintenance.
Further Reading & Resources
Empower your business with a system built for the modern era. At Basa, we specialize in high-performance enterprise operations management and ERP solutions that prioritize data integrity, seamless isolation, and scalable growth. Our architecture is designed to give you the security of a private vault with the speed and efficiency of the cloud.
Take the next step in your digital transformation:
- Explore our system: https://basa.pindah.org or https://basa.pindah.co.zw
- Call us today: +263714856897
- Email our experts: admin@pindah.org